NETWORK SECURITY & ADMINISTRATION
Build IT. Connect IT. Protect IT. Join the IT field and equip yourself with the skills to build and connect computers globally, while safeguarding valuable information. In this class, you’ll explore the realms of installing and managing operating systems (Windows & Linux), user support, virtual computing, managing cloud servers, and paving the way for a dynamic career in the ever-evolving field of technology. IT offers great salaries in a growing industry with remote working opportunities. Ask about Cyber Patriot, the Oklahoma Cup, and esports.
JOIN THE I.T. FIELD
Joining the Information Technology (IT) field can be an excellent career choice for those who enjoy working with technology, problem-solving, and staying up to date with the latest advancements. The IT field is rapidly growing and evolving, providing endless opportunities for learning and professional development.
IT professionals are in high demand across various industries, and the field offers a range of career paths, including cybersecurity. With the increasing importance of technology in today’s world, IT provides a stable and rewarding career with room for growth and advancement.
BUILD I.T.
It’s important to develop a good foundation in building computers and servers before you’re in charge of configuring a network. In this class you will gain the hardware fundamentals:
- Configure and support PC, mobile and IoT device hardware
- Configure device operating systems, including Windows, Linux, Android and iOS
- Troubleshoot and problem solve service and support challenges
- Implement basic data backup and recovery methods
PROTECT I.T.
Now that we have connected almost every device in our homes and offices to the Internet, we must consider what information is on these devices and what we can do to secure these devices.
Here are some of the information being sought after by hackers, businesses, and sometimes governments:
- Personal information used in ID theft like SSN, DOB, Usernames and Passwords
- Financial information like credit card numbers, bank account, and retirement information
- Company information like intellectual property, trade secrets, and customer information
- Encrypting data and holding it for ransom
CONNECT I.T.
Not too long ago, people had computers without internet access. That’s hard to imagine today.
With technology changing so rapidly, consumers are moving from hardwired to wireless connections on their devices. Although this doesn’t change the need for hardwiring the infrastructure and the server, the shift from desktops to mobile devices has its own infrastructural operation requirements.
Using a wireless mesh-network you can communicate with the network through a series of access points. These components seamlessly deliver, and shift wi-fi access points as needed. Here’s a few places you may have seen this work in action:
- Restaurants allow for paying the bill right from your table
- Retail stores use point of sale (POS) systems to do inventory and automatically reorder
- Remote workers and students access distant learning through Zoom and other apps supported by it
- Doctors carry a laptop from one patient room to another and constantly update patient records
- Casinos network floor games and know when a machine pays out
- Thermostats in all Walmart stores are controlled through the headquarters in Bentonville
“A large part of my employment came from having actual hands-on experience and continued learning. Professional dress lectures were also helpful, as well as understanding what employers look for in an interview. I got extremely lucky taking a job with Lumen Technologies right before COVID lockdowns. It allowed me to keep my family afloat when my husband was furloughed. I’m very happy and thankful for how far I’ve come thanks to the knowledge and confidence I gained at Central Tech.”
MAKE AN IMPACT ON INDIVIDUAL, CORPORATE, AND NATIONAL SECURITY
Americans love their technology, and the internet has transformed our lives. Most of them in good ways, however, it has also increased the number of security threats.
Americans spend nearly 5.5 hours a day on their phones with millennials spending 5.7 hours per day. That number jumps to nearly 7.5 hours a day for teens. Surprisingly, these numbers don’t reflect all screen time.
We are constantly on devices, whether it be desktop, laptop, or mobile. We are plugging in personal information, saving passwords, and trusting the system.
But who makes sure the system is trustworthy?
Who understands the virtual environment?
YOUR TRUSTY NEIGHBORHOOD CYBER SECURITY GURUS!
Are you interested in becoming the first line of defense against unauthorized access to computers, the protector from hackers and malicious software?
It’s not just individuals at risk. Network security is crucial to business success. Network systems protect and safeguard information as they minimize client information theft, secure shared files, protect against viruses, comply with regulatory requirements, and increase network performance.
Our network security program begins with the basics of computers (internal components, software). Then we move on to computer repair and networking. Security measures are integrated into all aspects of the program.
“Central Tech prepared me for the I.T. field with easy-to-learn concepts and provided me many opportunities.”
“I learned multiple software and operating systems and earned two Microsoft certifications.”
NETWORK SECURITY COMPLIANCE TECHNICIAN
PATHWAY
DETAILS
This program prepares you to maintain and administer computer networks and related computing environments including:
- Computer Hardware
- Systems Software
- Applications Software
- All Configurations
You will learn to diagnose, troubleshoot, and resolve hardware, software, or other network and system problems, and replace defective components when necessary. You will also learn how to safeguard computers, networks and servers from accidental or unauthorized modification, destruction, or disclosure.
AREAS OF STUDY
- Computer Repair
- Networking
- Network Security
- Windows Administration
- Windows Security
- Linux Administration
- Linux Security
- Capstone/Internship
“The most valuable thing I learned was how to enjoy learning. This has benefitted me tremendously in my current workplace.”
“I use everything I learned at Tech. It’s an exceptional program with amazing instructors. The coursework is exactly what you need for industry.”
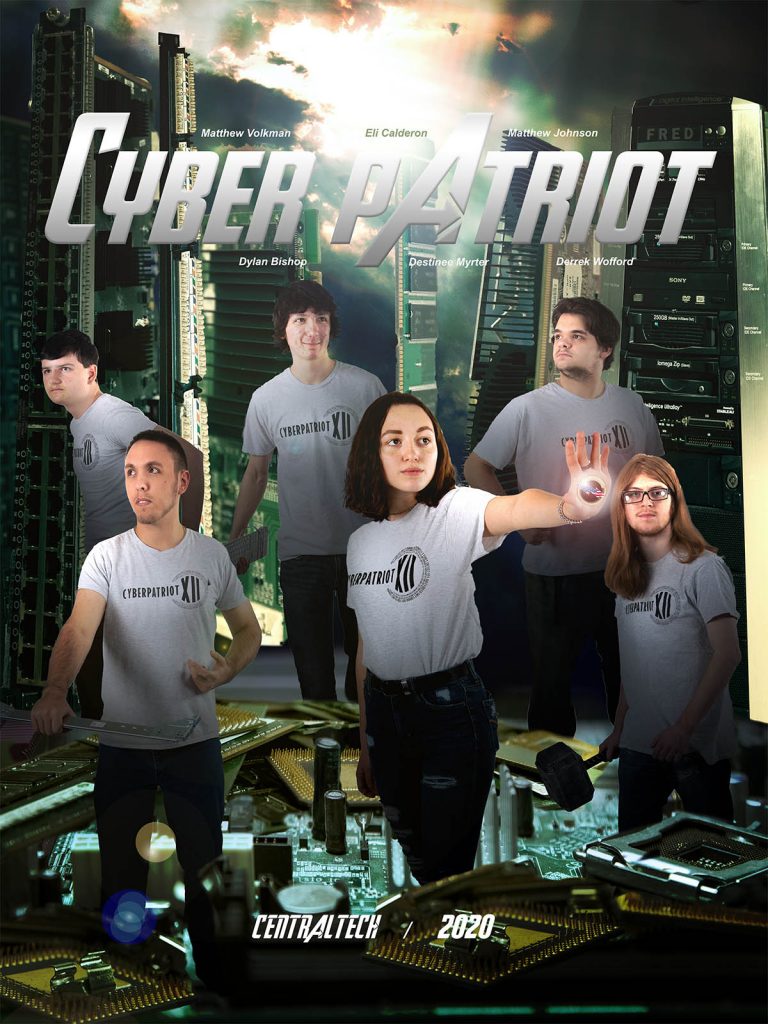
CYBERPATRIOT
The network security class competes annually in the world’s largest cybersecurity competition. The network challenge involves finding and fixing security vulnerabilities in Windows and Linux operation systems. The Cisco challenge contains an online quiz and a virtual networking exercise based on specific training material. We have had teams place in the final competition!
#centraltechNSA
[instagram-feed feed=15]
MORE INFORMATION
There is a global demand for cybersecurity talent. In fact, the job outlook is expected to grow by 32%. The average salary for “cybersecurity technician” ranges from $69,996 to $152,787 and continues to be a great field with high-paying jobs.
The computer and IT industry will continue to grow as spending on services, infrastructure, and software continue to trend upward. This is great news for our graduates as they have two options. Go to work, or go to college if you are interested in the management pathway.
Since companies hire based on your industry credentials, more and more students prefer going straight to work. They start gaining experience and making money immediately. In addition, many companies assist with college tuition. Graduates find by working and taking advantage of tuition assistance they:
- save thousands of dollars on student loans,
- gain experience as they are earning a degree,
- graduate college with employment, and
- work experience plus a degree earns them more income.
Our graduates find careers in a variety of industries with the top ones in health and energy. Some use their knowledge in the military while others work for large real estate companies.
- Certiport:
- IT Specialist – Cybersecurity
- IT Specialist – Networking
- IT Specialist – Network Security
- IT Specialist – Device Configuration and Management
- CompTIA:
- A+
- Linux+
- Network+
- Security+
- Cisco:
- CCNA
- CCST Cybersecurity
- Students: Adult & High School
- Campus: Drumright, Sapulpa
- Times: Morning, Afternoon, Full Day
- School Year: August-May
Ask about Financial Aid and Scholarship availability.